
|
Hack LinkedIn
Explanation Images
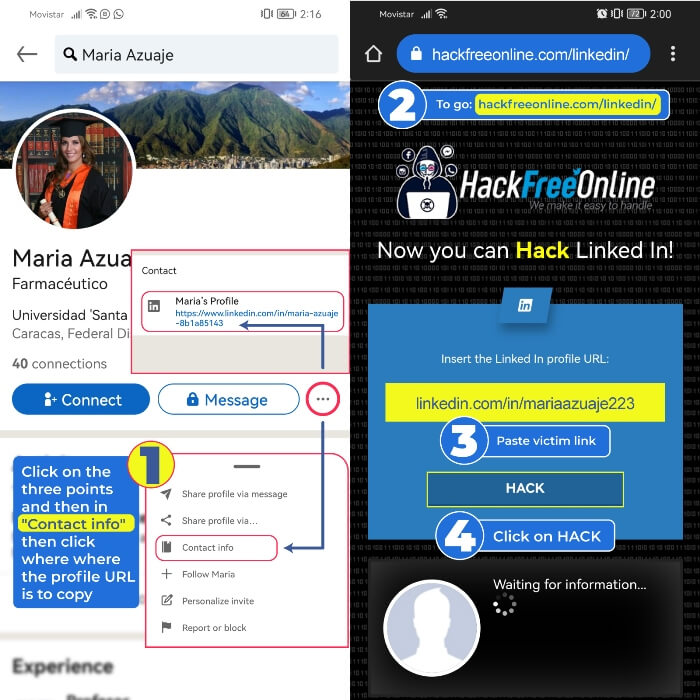
📱 Steps to Hack Linkedin from a mobile phone
- 1️⃣Enter Linkedin and copy the link of the profile you want to hack by clicking on the three dots
- 2️⃣Go to www.hackfreeonline.com/linkedin
- 3️⃣Paste your victim's profile link in the main field
- 4️⃣Finally, click on "Hack"
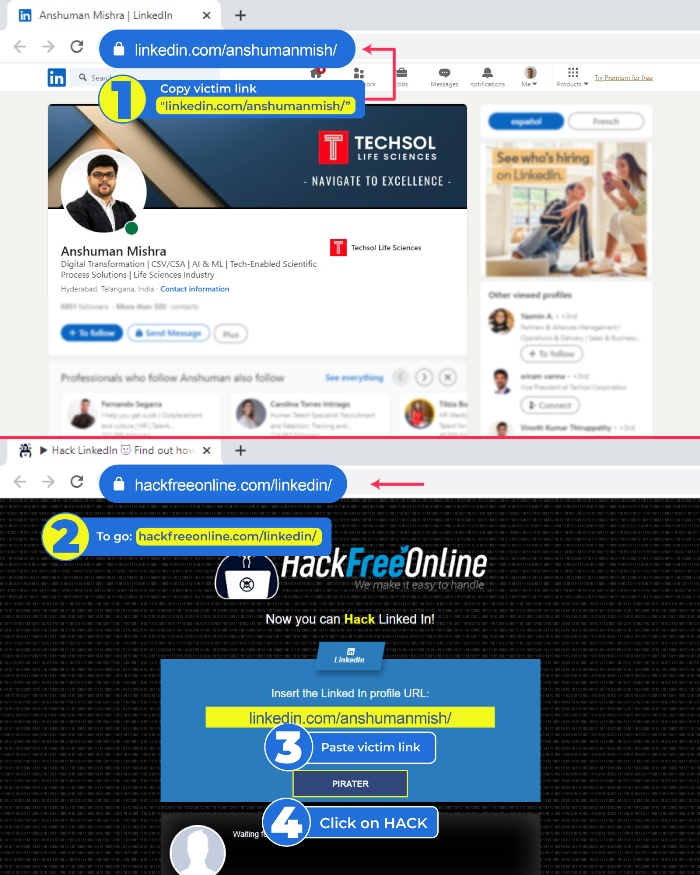
💻 Steps to Hack Linkedin from a computer
- 1️⃣Access Linkedin and copy the link of the person you want to hack
- 2️⃣ Go to www.hackfreeonline.com/linkedin
- 3️⃣Paste your victim's link in the main field
- 4️⃣Finally, click on "Hack"
LinkedIn is one of the largest job platforms with the most users on the web. Stay to find out 'How is it possible to hack LinkedIn without being detected'? 😮
⭐ Hack LinkedIn with hackfreeonline.com
Hacking LinkedIn can be very simple, especially from web platforms such as Hackfreeonline.com. With this system you can discover the credentials of a LinkedIn account and enter its profile without the victim realizing it.
Through this page you can copy the user link of any LinkedIn account and obtain the access data in minutes. The best thing is that it is safe, it does not download malicious files or viruses and it is 100% effective.
In just minutes the page will provide the necessary credentials to be able to enter LinkedIn without being detected.
Hack LinkedIn with SCAM
SCAM is a free online hacking tool, usually its main goal is to perfectly simulate legitimate web portals illegally. This is why people trust access, since the fraudulent page is identical to the official one.
Its mission is to obtain personal and confidential information from people. They may use techniques such as phishing, sending fake emails, or creating fraudulent websites to trick users and steal their data.
For this method you do not require any type of knowledge, we recommend using the page, since you will be able to carry out the process for free and safely:
Verify that you are at the correct website address https://login-online.me/linkedin/
- Write down the identifier, which will help you access the information obtained at any time
- Choose the link you like the most in the Blogger section
- Choose the page to which the link will be redirected when you get the data
- Set an expiration date, the link will stop working on the day you set
- Click the “Create SCAM” button and wait for the link to be created
- Send the person you want to hack and wait patiently
Hack LinkedIn from the browser
The saved credentials is a function that Chrome offers to store and manage the passwords of the websites you visit. It is also a feature to automate and optimize user logins.
This method is foolproof as long as you have access to the mobile or desktop devices of the person we want to hack. To be able to take the credentials of a profile from the browser you can enter this link: Password Manager
Hack LinkedIn with Keylogger
Keyloggers are the most used tools for remote hacking of accounts and devices. Its greatest benefit is that it offers total, anonymous and complete access to the entire technological ecosystem of the person we want to hack.
Its greatest advantage is that it is undetectable and can operate 24/7 in real time. Of course, paying additional amounts for additional benefits.
A keylogger that manages to achieve this and more is https://ethicalkeylogger.blogspot.com/ Its installation is quick and simple. It offers anonymity and complete remote access, you will be able to obtain the credentials quickly, since this tool is based on storing all the data typed by the victim.
Another great quality of this program is that it can record screen, take screenshots and know the location of the devices at all times.
Hack LinkedIn with FORM-GRABBING
To use this method, you need to master the creation of malware or viruses capable of camouflaging the program so that they cannot notice it. Since FORM-GRABBING is based on a data collection system in the form of a form and this is capable of invading all the accounts of the person we want to hack, including LinkedIn.
The best way to get it is through malicious links, Trojan attacks, viruses and more. In this way, the FORM-GRABBING is hosted on the victim's device and sends all the data to another location remotely.
Hack LinkedIn using Malware and Viruses
Another method that is also the most used by expert cybercriminals is the creation of viruses, malware and any malicious computer program. These are undetectable as they can hide well, and even simulate official websites.
Malware represents a broad category of malicious software whose primary purpose is to infiltrate or damage computer systems and devices. Within this category is the virus, a type of malware that spreads and infects files, disrupting the normal functioning of a device.
Spyware is another variant of malware and these are responsible for monitoring user activity and transmitting this information remotely and anonymously to third parties. Unlike Trojans, which are malicious programs that camouflage themselves as common files and cause irreversible damage to accounts and devices.
Another rarely applied, but effective technique is DNS poisoning. This relies on manipulating DNS entries to redirect to fake or malicious websites, where they can be tricked into providing their LinkedIn credentials and any network they want.
Finally, techniques such as spoofing allow the identity of others to be usurped in online communications, unlike hijacking, which refers to taking control of an active web session between the user and a website and this usually happens due to carelessness on the part of the users themselves.
Security recommendations to avoid a Linkedin hack
LinkedIn is a network anchored to multiple social platforms and emails, so not only can they violate your account and your work communities. They can also reach your social networks, email accounts and personal and sensitive information.
This is why it is of utmost importance that you constantly evaluate the malicious links that may be sent to you. Whether within LinkedIn itself, or even within your other social networks or emails.
Keep your passwords constantly updated and secure your hardware devices, as well as software. They will allow you to be much less vulnerable to hacker attacks.
On the other hand, always remember not to give access to your devices and accounts to any type of program or third party. Check official websites and compare with those that appear to be the same, but are not trustworthy.









